April 28, 2022
As part of this month’s Continuing Privacy and Security Training (“CPST”), The Compliance Team sought to explain ” 5 Common Phishing Attacks and How to Protect Against Them”
What is Phishing?
Phishing is a type of cybersecurity attack during which malicious actors send messages pretending to be a trusted person or entity. Phishing messages manipulate a user, causing them to perform actions like installing a malicious file, clicking a malicious link, or divulging sensitive information such as access credentials. Phishing is the most common type of social engineering, which is a general term describing attempts to manipulate or trick computer users. Social engineering is an increasingly common threat vector used in almost all security incidents. Social engineering attacks, like phishing, are often combined with other threats, such as malware, code injection, and network attacks.
Common Phishing Attacks and How to Protect Against Them
1. Deceptive Phishing
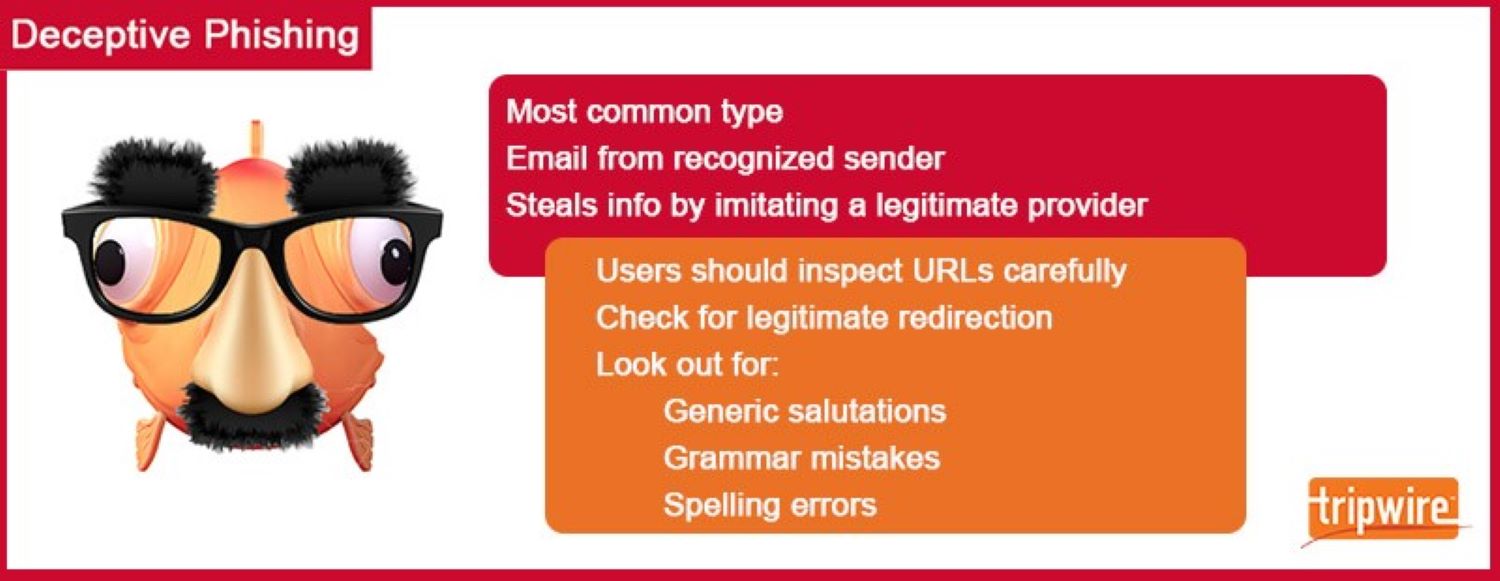
Deceptive phishing is the most common type of phishing scam. In this ploy, fraudsters impersonate a legitimate company to steal people’s personal data or login credentials. Those emails use threats and a sense of urgency to scare users into doing what the attackers want.
Techniques Used in Deceptive Phishing
Some of most common techniques used in deceptive phishing attacks. These are as follows:
• Legitimate links – Many attackers attempt to evade detection from email filters by incorporating legitimate links into their deceptive phishing emails. They could do this by including contact information for an organization that they might be spoofing.
• Blend malicious and benign code ¬¬– Those responsible for creating phishing landing pages commonly blend malicious and benign code together to fool Exchange Online Protection (EOP). This might take the form of replicating the CSS and JavaScript of a tech giant’s login page to steal users’ account credentials.
• Redirects and shortened links – Malicious actors don’t want to raise any red flags with their victims. They therefore use shortened URLs to fool Secure Email Gateways (SEGs). They also use “time bombing” to redirect users to a phishing landing page only after the email has been delivered. After victims have forfeited their credentials, the campaign then redirects victims to a legitimate web page.
• Modify brand logos – Some email filters can spot when malicious actors steal organizations’ logos and incorporate them into their attack emails or onto their phishing landing pages. They do so by looking out for the logos’ HTML attributes. To fool these detection tools, malicious actors alter an HTML attribute of the logo such as its color.
• Minimal email content – Digital attackers attempt to evade detection by including minimal content in their attack emails. They might elect to do this by including an image instead of text, for instance.
How to Defend Against Deceptive Phishing
The success of a deceptive phish hinges on to what extent an attack email resembles official correspondence from a spoofed company. Acknowledging that fact, users should inspect all URLs carefully to see if they redirect to an unknown and/or suspicious website. They should also look out for generic salutations, grammar mistakes, and spelling errors.
2. Spear Phishing

Not all phishing scams embrace “spray and pray” techniques. Some ruses rely more on a personal touch. They do so because they wouldn’t be successful otherwise. That’s the logic behind spear phishing schemes.
In this type of ploy, fraudsters customize their attack emails with the target’s name, position, company, work phone number, and other information to trick the recipient into believing that they have a connection with the sender. Yet the goal is the same as deceptive phishing: get the victim into clicking on a malicious URL or email attachment so that they’ll hand over their personal data. Given the amount of information needed to craft a convincing attack attempt, it’s no surprise that spear-phishing is commonplace on social media sites like LinkedIn where attackers can use multiple data sources to craft a targeted attack email.
Techniques Used in Spear Phishing
Provided below are some of the most common techniques used in spear phishing attacks:
• Housing malicious documents on cloud services: CSO reported that digital attackers are increasingly housing malicious documents on Dropbox, Box, Google Drive, and other cloud services. By default, IT is not likely to block these services, which means the organization’s email filters won’t flag the weaponized docs.
• Compromise tokens: CSO also noted that digital criminals are attempting to compromise API tokens or session tokens. Success in this regard would enable them to steal access to an email account, SharePoint site, or other resource.
• Gather out-of-office notifications: Attackers need lots of intelligence to send a convincing spear-phishing campaign. Per Trend Micro, one way they can do this is by emailing employees en masse and gathering out-of-office notifications to learn the format of the email addresses used by internal employees.
• Explore social media: Malicious actors need to learn who’s working at a targeted company. They can do this by using social media to investigate the organization’s structure and decide whom they’d like to single out for their targeted attacks.
How to Defend Against Spear Phishing
To protect against this type of scam, organizations should conduct ongoing employee security awareness training that, among other things, discourages users from publishing sensitive personal or corporate information on social media. Companies should also invest in solutions that analyze inbound emails for known malicious links/email attachments. This solution should be capable of picking up on indicators for both known malware and zero-day threats.
3. Whaling
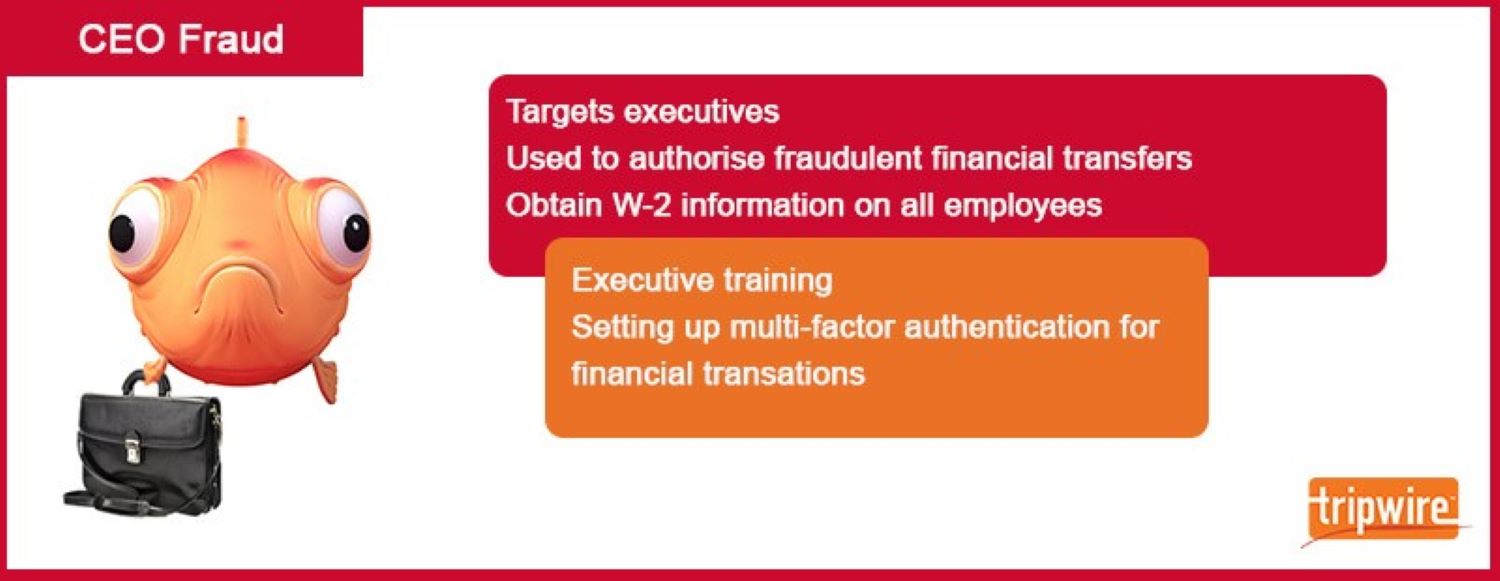
Spear phishers can target anyone in an organization, even executives. That’s the logic behind a “whaling” attack. In these scams, fraudsters try to harpoon an exec and steal their login details.
In the event their attack proves successful, fraudsters can choose to conduct CEO fraud. CEO fraud is when attackers abuse the compromised email account of a CEO or other high-ranking executive to authorize fraudulent wire transfers to a financial institution of their choice. Alternatively, they can leverage that same email account to conduct W-2 phishing in which they request W-2 information for all employees so that they can file fake tax returns on their behalf or post that data on the dark web.
Techniques Used in Whaling
Whaling attacks commonly make use of the same techniques as spear phishing campaigns. Here are a few additional tactics that malicious actors could use:
• Infiltrate the network: A compromised executive’s account is more effective than a spoofed email account. As noted by Varonis, digital attackers could therefore use malware and rootkits to infiltrate their target’s network.
• Follow up with a phone call: The United Kingdom’s National Cyber Security Centre (NCSC) learned of several instances where attackers followed up a whaling email with a phone call confirming the email request. This social engineering tactic helped to assuage the target’s fears that there could be something suspicious afoot.
• Go after the supply chain: Additionally, the NCSC has witnessed a rise of instances where malicious actors have used information from targets’ suppliers and vendors to make their whaling emails appear like they’re coming from trusted partners.
How to Defend Against Whaling
Whaling attacks work because executives often don’t participate in security awareness training with their employees. To counter the threats of CEO fraud and W-2 phishing, organizations should mandate that all company personnel—including executives—participate in security awareness training on an ongoing basis.
Organizations should also consider injecting multi-factor authentication (MFA) channels into their financial authorization processes so that no one can authorize payments via email alone.
4. Vishing
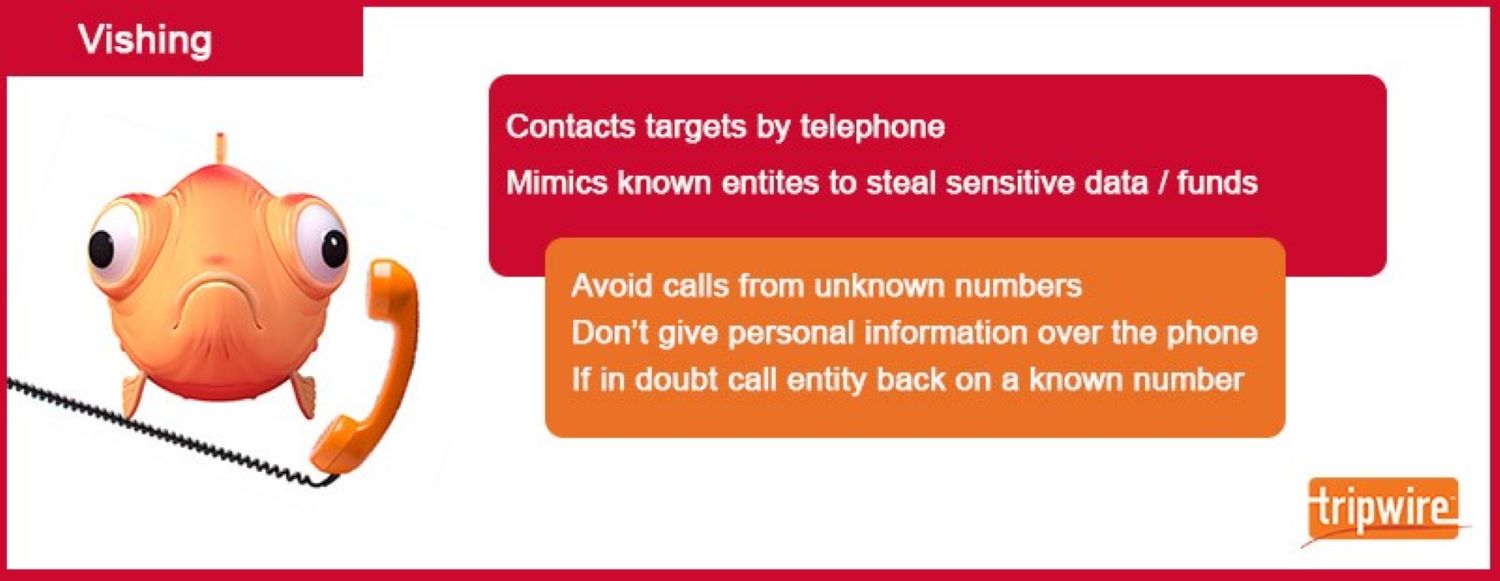
Until now, we’ve discussed phishing attacks that for the most part rely on email. But fraudsters do sometimes turn to other media to perpetrate their attacks.
Take vishing, for example. This type of phishing attack dispenses with sending out an email and goes for placing a phone call instead. Vishing scams involve automated phone calls pretending to be from a trusted entity, asking the victim to type personal details using their phone keypad.
Techniques Used in Vishing
Here are some common techniques used in vishing attacks:
• “The mumble technique”: Digital attackers will oftentimes incorporate unique tactics to go after specific targets. For instance, as reported by Social-Engineer, LLC, when they attempt to target customer service representatives or call center agents, malicious actors might use what’s known as “the mumble technique” to mumble a response to a question in the hopes that their “answer” will suffice.
• Technical jargon: If malicious actors are targeting a company’s employees, Social-Engineer, LLC noted that they might impersonate in-house tech support by using technical jargon and alluding to things like speed issues or badging to convince an employee that it’s okay for them to hand over their information.
• ID spoofing: Here, a malicious actor disguises their phone number to make their call look like it’s coming from a legitimate phone number in the target’s area code. Twinstate noted that this technique could lull targets into a false sense of security.
How to Defend Against Vishing
To protect against vishing attacks, users should avoid answering calls from unknown phone numbers, never give out personal information over the phone, and use a caller ID app.
5. Smishing
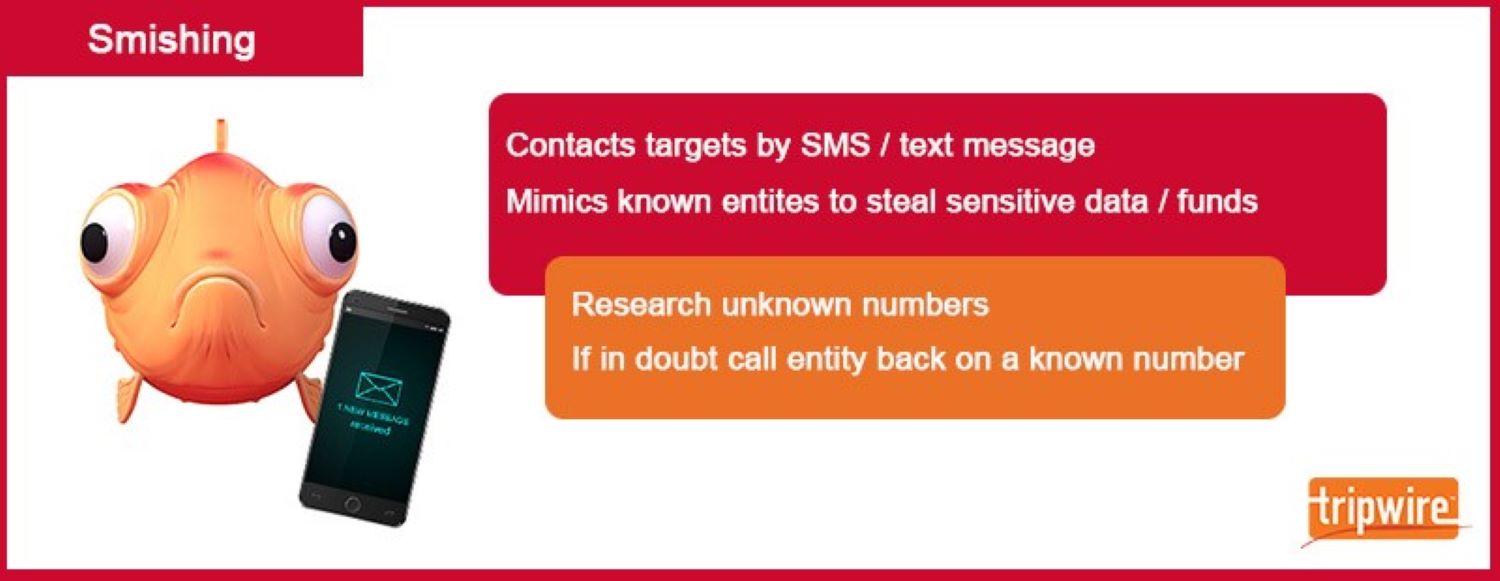
Vishing isn’t the only type of phishing that digital fraudsters can perpetrate using a phone. They can also conduct what’s known as smishing. This method leverages malicious text messages to trick users into clicking on a malicious link or handing over personal information.
Techniques Used in Smishing
Webroot identified some techniques commonly used by smishers:
• Trigger the download of a malicious app: Attackers can use malicious links to trigger the automatic download of malicious apps on victims’ mobile devices. Those apps could then deploy ransomware or enable nefarious actors to remotely control their devices.
• Link to data-stealing forms: Attackers could leverage a text message along with deceptive phishing techniques to trick users into clicking a malicious link. The campaign could then redirect them to a website designed to steal their personal information.
• Instruct the user to contact tech support: With this type of attack tactic, malicious actors send out text messages that instruct recipients to contact a number for customer support. The scammer will then masquerade as a legitimate customer service representative and attempt to trick the victim into handing over their personal data.
How to Defend Against Smishing
Users can help defend against smishing attacks by researching unknown phone numbers and by calling the company named in suspicious SMS messages if they have any doubts.
As always, please let the eHealth Technologies’ Privacy and Security Compliance Team know if you have any questions on the privacy and security of Covered Information, including PHI, ePHI, and other Confidential Information.
Thank you for Caring Together…
eHT Compliance Team
Abdul Nazeer Uddin
IT Security Engineer | eHealth Technologies
Abdul.nazeeruddin@ehealthtechnologies.com
Mobile: +91 8639879748