As part of this month’s Continuing Privacy and Security Training (“CPST”), the Compliance Team wanted to describe “What is Ransomware Attack?”
What is Ransomware Attack?
Ransomware is a type of malware attack in which the attacker locks and encrypts the victim’s data, important files and then demands a payment to unlock and decrypt the data.
This type of attack takes advantage of human, system, network, and software vulnerabilities to infect the victim’s device—which can be a computer, printer, smartphone, wearable or other endpoint.
How Does Ransomware Work?
After a device is exposed to the malicious code, the ransomware attack proceeds as follows. Ransomware can remain dormant on a device until the device is at its most vulnerable, and only then execute an attack.
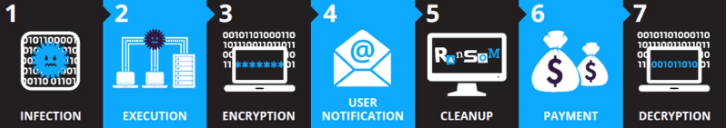
- Infection—Ransomware is covertly downloaded and installed on the device.
- Execution—Ransomware scans and maps locations for targeted file types, including locally stored files, and mapped and unmapped network-accessible systems. Some ransomware attacks also delete or encrypt any backup files and folders.
- Encryption—Ransomware performs a key exchange with the Command and Control Server, using the encryption key to scramble all files discovered during the Execution step. It also locks access to the data.
- User Notification—Ransomware adds instruction files detailing the pay-for-decryption process, then uses those files to display a ransom note to the user.
- Clean up—Ransomware usually terminates and deletes itself, leaving only the payment instruction files.
- Payment—Victim clicks a link in the payment instructions, which takes the victim to a web page with additional information on how to make the required ransom payment. Hidden TOR services are often used to encapsulate and obfuscate these communications to avoid detection by network traffic monitoring.
- Decryption—After the victim pays the ransom, usually via the attacker’s Bitcoin address, the victim may receive the decryption key. However, there is no guarantee the decryption key will be delivered as promised.
Ransomware Distribution Techniques.
The device is infected when the victim clicks a link, visits a web page, or installs a file, application, or program that includes malicious code designed to covertly download and install the ransomware. This can happen in a variety of ways:
| Distribution Techniques | Description |
| Phishing email | Clicking a link embedded in an email, which redirects to a malicious web page. |
| Email attachments | Opening an email attachment and enabling malicious macros; or downloading a document embedded with a Remote Access Trojan (RAT); or downloading a ZIP file containing a malicious JavaScript or Windows Script Host (WSH) file. |
| Malvertising | Clicking a legitimate advertising site seeded with malicious code. |
| Infected programs | Installing an application or program containing malicious code. |
| Self-propagation | Spreading the malicious code to other devices through network and USB drives. |
Ransomware Protection for your Personal Computer
Here are several best practices that can help you prevent and protect against Ransomware infections::
Endpoint Protection
Antivirus is an obvious first step in ransomware protection, but legacy antivirus tools can only protect against some ransomware variants.
Data Backup
Regularly backup data to an external hard-drive or the cloud, using versioning control and the 3-2-1 rule (create three backup copies on two different media with one backup stored in a separate location). If possible, disconnect the hard-drive from the device to prevent encryption of the backup data.
Patch Management
Keep the device’s operating system and installed applications up-to-date, and install security patches. Run vulnerability scans to identify known vulnerabilities and remediate them quickly.
Email Protection
Learn to recognize social engineering emails and phishing. Use spam protection and endpoint protection technology to automatically block suspicious emails, and block malicious links if user does end up clicking on them.
Ransomware Attack Examples
Below we list a few malware examples that made a global impact and caused widespread damage.
- WannaCry
WannaCry is an encrypting ransomware that exploits a vulnerability in the Windows SMB protocol, and has a self-propagation mechanism that lets it infect other machines. WannaCry is packaged as a dropper, a self-contained program that extracts the encryption/decryption application, files containing encryption keys, and the Tor communication program. It is not obfuscated and relatively easy to detect and remove. In 2017 WannaCry spread rapidly across 150 countries, affecting 230,000 computers and causing an estimated $4 billion in damages.
- Crypto locker
Crypto locker was released in 2017, and affected over 500,000 computers. It typically infects computers through email, file sharing sites, and unprotected downloads. It not only encrypts files on the local machine, but can also scan mapped network drives, and encrypt files it has permission to write to. New variants of Crypolocker are able to elude legacy antivirus software and firewalls.
- Cerber
Cerber is ransomware-as-a-service (RaaS), and is available for use by cybercriminals, who carry out attacks and spread their loot with the malware developer. Cerber runs silently while it is encrypting files, and may try to prevent antivirus and Windows security features from running, to prevent users from restoring the system. When it successfully encrypts files on the machine, it displays a ransom note on the desktop wallpaper.
- Locky
Locky is able to encrypt 160 file types, primarily files used by designers, engineers and testers. It was first released in 2016. It is primarily distributed by exploit kits or phishing—attackers send emails that encourage the user to open a Microsoft Office Word or Excel file with malicious macros, or a ZIP file that installs the malware upon extraction.
Ransomware Removal: How to Mitigate an Active Ransomware Infection
If you detect a Ransomware infection in your home network, here are the immediate steps you should take to mitigate the ransomware threat:
- Isolate – Identify infected machines, disconnect from networks and lock shared drives to prevent encryption.
- Investigate – See what backups are available for encrypted data. Check what strain on ransomware you were hit with, and if there are decryptors available. Understand if paying the ransom is a viable option.
- Recover – If no decryptor tools are available, restore your data from backup. In most countries, the authorities do not recommend paying the ransom, but this may be a viable option in some extreme cases. Use standard practices to remove ransomware or wipe and reimage affected systems.
- Reinforce – Run a lessons learned session to understand how internal systems were infected and how to prevent a recurrence. Identify the key vulnerabilities or lacking security practices that allowed the attackers in, and remediate them.
- Evaluation – Once the crisis has passed, it’s important to evaluate what happened and the lessons learned. How was ransomware successfully executed? Which vulnerabilities made penetration possible? Why did antivirus or email filtering fail? How far did the infection spread? Was it possible to wipe and reinstall infected machines, and were you able to successfully restore from backup? Address the weak points in our security posture to be better prepared for the next attack.